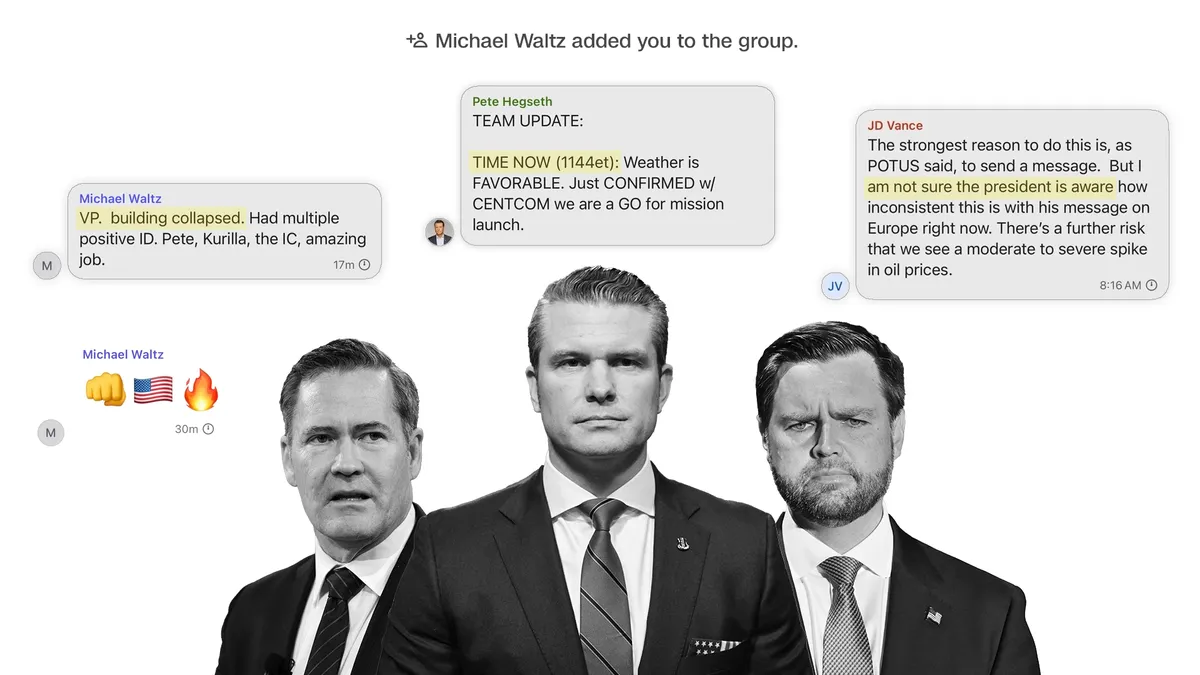
In a recent development, National Security Adviser Mike Waltz revealed that he added Jeffrey Goldberg, the editor-in-chief of The Atlantic, to a group chat intended for coordination purposes. This revelation has ignited significant debate regarding the protocols of communication among top national security officials. During an interview on Fox News, Waltz took full responsibility for the creation of the group chat but attempted to distance himself from Goldberg's inclusion, suggesting that Goldberg might have improperly inserted himself into the conversation—a claim that raises questions given the known operating system of Signal, the messaging platform used.
Waltz stated, “Now, whether he did it deliberately or it happened in some other technical mean is something we’re trying to figure out.” He further implied that the situation might have arisen from a simple mix-up with contact names on his phone. “Have you ever had someone’s contact that shows their name, and then you have someone else’s number associated with it?” he questioned, trying to explain why he didn’t recognize Goldberg's name in the group. This incident has sparked a fascinating debate among top administration officials about the implications of military action against the Houthis, an Iran-backed group that has intensified attacks on international shipping amid ongoing conflicts in Gaza.
Senator Josh Vance has been vocal about his perspective on the domestic political ramifications of potential strikes against the Houthis. His assertions that former President Donald Trump may not have been fully briefed on how these strikes could contradict his current foreign policy messages regarding Europe have raised eyebrows throughout Washington. Initially, this became the primary focus of the White House's public stance on the matter. However, a spokesperson for Vance later clarified that both the President and Vice President are in complete agreement regarding the situation.
Both the Biden and Trump administrations have faced challenges in curbing Houthi strikes on international shipping, an issue the group claims is a defensive measure for Palestinians in Gaza. The Biden administration has conducted multiple airstrikes against the Houthis, including the use of stealth B-2 bombers. Historically, Trump also ordered several strikes against the group, although the military has not disclosed specific impacts on Houthi leadership or their arsenal.
Recently, a second aircraft carrier was deployed to the region, with Waltz emphasizing that European nations lack the naval capabilities necessary to secure vital shipping lanes. He suggested that the Trump administration intended for European countries to contribute financially to these military operations, aligning with Trump’s broader call for allied nations to shoulder more defense costs.
Despite assertions from senior officials that nothing discussed in the group chat was classified, multiple defense sources have indicated that at least some of the operational details shared were highly sensitive at the time of transmission. The Houthi rebels are known to possess anti-aircraft weaponry, raising concerns about the potential risks to American personnel. The Signal app, while end-to-end encrypted, is not sanctioned for classified discussions, exposing a significant vulnerability in the communication of sensitive information among national security officials.
This incident underscores the ongoing debate over the handling of classified information within the Trump administration. If not for the text sent by Pete Hegseth, the focus might have remained on the foreign policy implications of the discussions rather than the potential mishandling of sensitive operational data. The national security adviser's after-action report, delivered in real time, further complicates the narrative, as military damage assessments are typically released only after careful scrutiny to avoid compromising intelligence sources and methods.
As this situation unfolds, it highlights the critical need for secure communication channels among national security officials and poses questions about the protocols in place for sharing sensitive information, especially in high-stakes military contexts.